Microsoft Office 365 prides itself on enabling dynamic, collaborative workplaces for its customers. Industry leading security measures, and attention to privacy, compliance, and accessibility, support the robust functionality of the cloud productivity suite. Even so, research shows that data loss and protection, are still major concerns for most businesses migrating to the cloud.
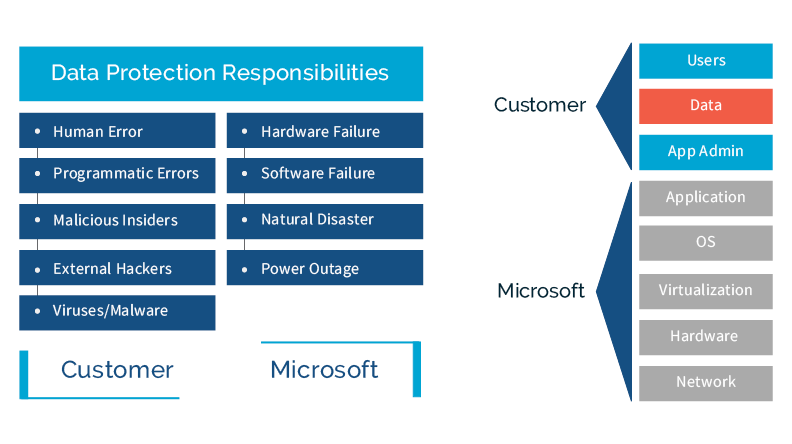
Part of that worry can be alleviated by having secure backups of SaaS data, and the ability to quickly restore that data to an application in the event of data loss. This post will examine a few important backup policies offered by Office 365 so that you can determine where Microsoft’s responsibilities regarding backup and recovery end. Where do yours begin. Equipped with this knowledge, you can feel confident that you can fully protect Office 365 data, wielding the power of the cloud without worry over data loss.
Data loss is often a major concern for Office 365 customers. Microsoft’s backup policies cannot guarantee a complete and speedy restore of lost data. Even when data is retrievable, the process is long and complicated. Retention policies vary for each application included in the cloud platform.
Backup and retention policies are not a substitute for a complete backup and restore solution.
Even more importantly, Microsoft’s policies are not designed so that customers have direct access to backed up data with the ability to easily restore it.
Contact us Today, to see how we can keep your 365 Data secure and backed up.